M2SYS Biometric Technology Infographics
A major M2SYS goal is educating the marketplace about the value of biometric technology. Infographics provide key data visualization tools to help understand industry environments and illustrate conditions where biometric identification tools can help.
Application of Biometrics:
How biometrics can protect your business
The top seven advantages of a biometric identification management system
Infographics: 10 massive biometric technology examples that revamped the world
Infographics: why you need biometric visitor management system for schools?
Healthcare Biometrics:
Patient misidentification and its impacts on patient experience
Health systems and hospitals are adversely affected financially which are linked to patient misidentification. On average, 35% of all denied claims are due to patient misidentification or lack of patient information. This problem alone costs any given healthcare facility a whopping $1.2 million per year! Moreover, 76% of the sample believe that denied claims could be reduced with the help of a biometric patient identification system.
That was all about the financial impact, but what about the impact on the patient experience?
Patient experience is adversely affected due to patient matching errors, generating longer patient waiting times. In fact, 69% said that a minimum of 30 minutes or more is needed to retrieve crucial patient information from medical records or the HIM department. This negatively impacts productivity since patients need to wait longer to then receive healthcare services.
Overall, patient misidentification causes all sorts of problems for any given healthcare provider, regardless of its size or reputation. So, how are healthcare providers keeping up with the challenge? RightPatient is helping to solve the problems related to patient matching errors and thus speeding up the process, enhancing the patient experience, and reducing denied claims as well as reducing insurance fraud. It identifies patients within seconds using their biometrics like their irises or fingerprints, and then pulls the appropriate EHR- it’s that easy. RightPatient is the healthcare industry’s most versatile and scalable biometric patient identification and matching system, committed to enhancing the patient experience.
How common is patient misidentification?
A definition of patient identification and how can it be improved
Infographic on Iris Recognition vs. Retinal Scanning
How to setup an Iris Recognition Camera
5 benefits of using Iris Scanning Software in hospitals
To help you understand more about how an iris scanning software can help, this infographic presents the benefit of iris scanning software in a hospital.
The effect of fraud, theft and inaccurate patient identification on healthcare the effect of fraud theft and inaccurate patient identification on healthcare
Learn about common issues and problems healthcare encounters that cause pressure and strain on a system currently moving swiftly towards the adoption and implementation of electronic medical records. What solutions can help to stop medical identity theft, duplicate medical records, and an inaccurate patient identification system?
The cost of duplicate records and overlays in healthcare the cost of duplicate records and overlays in healthcare
This healthcare Infographic details the origins and costs of duplicate medical records and overlays plus provides a detailed look at the solutions in place to prevent their creation.
Workforce Management:
RightPunch – An affordable Kronos timekeeping system
5 benefits of using RightPunch – a biometric time clock for Kronos
5 ways your staff may be stealing time
How to eliminate ghost employee frauds by biometrics
Ghost employee fraud becomes a serious hindrance to many companies throughout the world. It costs hundreds of dollars every year that becomes burdensome to them. To the small companies to large organizations, ghost employee problem is ubiquitous and companies are looking for a viable solution.
How do employees steal time
How a biometric time clock improves workforce management
A biometric time clock is a viable solution to eliminate time theft and improve workforce management. The following Infographic demonstrates why biometric time clock deployments are increasing and what benefits employers can expect to see post implementation.
Biometric Modality Comparison:
Iris Recognition vs. Retinal Scanning: What are the differences? iris vs. retinal scanning – what are the differences between these two biometric modalities
A critical part of understanding biometric identification management technology is the ability to differentiate between hardware modalities and understand their capabilities and limitations. One of the most common misunderstandings in biometrics is the difference between iris recognition and retinal scanning, two separate modalities that have distinct characteristics which make them unique.
Government Solutions:
Infographic: Applications of AFIS
Governments around the world are adopting Automated Fingerprint Identification Systems (AFIS) for border control, law enforcement, public safety, voter registration, healthcare and welfare distribution, and national ID cards. Compared to traditional non-biometric identification systems, AFIS platforms have proven to be much more accurate and secure.
Cloud Biometric:
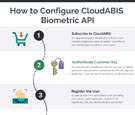
How to configure CloudABIS biometric API
If you are thinking of integrating a biometric identification system with your web or mobile application, this infographic will help you to do it within a few hours. For the convenience of your project, you can subscribe to any cloud-based biometric identification system like CloudABIS which is highly scalable, affordable that provides straightforward SaaS (Software-as-a-Service) pricing model.
Infographic: 3 ways of biometric authentication in web application
Common queries among developers often raise that if there is any way for biometric authentication in a web application. Yes, there are several ways and those are easy and simple too. You can do it in different ways as per your requirements, applications, budget, and expertise.
Visitor Management:
5 features to assess in a visitor management system
Organizations whether it is government or private, small or large, school or hospital, nowadays want to keep their premises safe and secure due to various incidents. An office premise not only has its employees but also visitors on a regular basis. A visitor might be a person who is there for a meetup, or for an interview; they might be a contractor, a lawyer, a supplier, anybody other than an employee is considered as a visitor on the office premise. To identify and verify these people as visitors, organizations now feel that the need for introducing a visitor management system.
Banking & Finance:
Best customer identification system for banking
Customer Identification in banking is known as KYC (Know Your Customer). The first step of the KYC process starts with identifying a customer and ends with complying other basic information like income, expenditure, tax information, foreign transaction, etc. Then the information is required to be verified by the due diligence team. According to the organizations need and the requirement of the organization, the KYC process is done by the customer relationship managers or directly by the Customer Due Diligence team. On the basis of these information institutions like banks or other company take the risk of financial transaction with their customers. So, choosing the best customer identification system or KYC tool is the most sensible decision for the organization.
Contact Us
Our knowledgeable sales consultants are located worldwide to answer any questions that you have about our identity management technology. Please complete the form below with as much information as you can so we are best prepared to assist you.