Biometrics: How does it Reduce the Risk of Security Breaches?
The following is a guest post by Robert Kramers.
In one way or another, biometrics has been around for a long time. Film fans may remember it from the 1993 film Demolition Man. This film is often cited as “predicting” the use of biometrics in security, but the truth is that this idea has been floating around since the discovery of fingerprints.
So, what is bio-security?
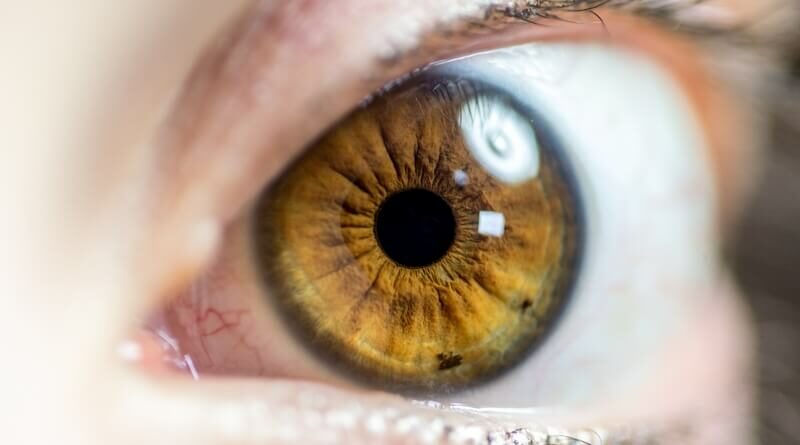
Bio-security uses biometrics as a way of identification and access control. It involves the use of body parts as an identification process, and works in a similar way we know fingerprint scanning works. An eye scanner, for instance, can detect all of the minute differences in the human eye, which are much more visible than people think, as evidenced by the photo below.
When it comes to biometric security, everything from your face to your DNA can be used to identify you. This technology is not just the stuff of science fiction anymore and biometric security and is currently used on consumer tablets and smartphones as well as access to sensitive information and hardware within high level corporations.
Biometrics has the potential to be used everywhere, from top-end businesses keeping entire buildings secure to artists, writers and photographers looking to secure the safety and protection of their intellectual property. Biosecurity is far more advanced than any other form of security, and contains fewer holes and breaches that leave more traditional systems vulnerable.
Fast Access to Personal Information
The main advantage of biometric technology over traditional security systems is that it detects things that are unique to the individual quickly and accurately.
This means that a place of business can ensure that only the employees gain access and attempted crime can be pinpointed faster.
Biometrics and a number of advancing technologies, including wireless power through resonant induction, have the ability to work cohesively. Items like this biometric sensor, which is printed directly on to human flesh (aka the biostamp) means, that a number of personally identifiable features has the ability to be obtained from the likes of a patient, in just seconds. Wireless power would provide the ability for the biostamp to communicate with internal devices like LVADs. This has the potential to help with medical information security, monitoring and identification.
Accuracy of Identification
Despite the misconception provided by popular sci-fi action movies, in real life modern biometric scanners detect capillary flow behind the eye or the finger, which means that they can only be used by a living, breathing person.
Biometrics can also be used to stop security holes that other systems can not detect.
For example, at Disney World, where a 5-day ticket can cost up to US$350, biometric fingerprint scanners are used to ensure that only the person who purchased a ticket can enter the park, which stops people from lending, sharing or even selling their ticket to others.

Absence of Anonymity
Every time an eye scanner, fingerprint scanner or any other form of biometric is used to allow access for one person, that person’s details can be stored in a database. Not only is their physiological data stored which can be used to find their name, address and more but also information on when and where they logged in.
By scanning for fingerprints, irises and other unique parts of an individual’s physiology, it ensures that it knows exactly who is trying to gain access at any given time.
This information can be used across the board, from employers who simply want to make sure their employees are logging in and doing their work when they should, to those investigating crimes on the premises.
Unauthorized Duplication
We live in an age where everything from luxury handbags to prescription medication can be copied to the finest details, and this also applies to keys and key cards, the very things that keep us secure using current security standards. The beauty of biometrics is the near impossibility of duplication.
As each individual is unique, and due to the complex nature of the biometric systems, moulds and other inanimate things cease to work.
Loss and Theft
Finally, whereas keys and codes can be lost, biometrics can not.
Simply put, you can’t lose you.
Not only does this mean that you will always have access, but it also guarantees that you are not leaving open access to your property on the subway or in the back of a taxi. Where your access is, you are also – which adds another layer of complexity and security to accessed gained.
In conclusion, the idea of biometrics and security have an increasing number reasons to be adopted particularly for reasons related to security. Additionally, it is very possible that some forms of biometric security like vein pattern recognition and eye scanning will have the ability to provide hygiene benefits due to non-contact biometric interpretation.
















Once your electronically stored biometric data which must be stored as a
file like all passwords or security measures is stolen you will be compromised for the rest of your life. You can not change your fingerprints or iris and whoever stole the file can now save it on a illegal credit card or in an IPhone and pretend to be you forever!
Thanks for your feedback on this. I would like to clarify by saying that there are solutions available which does not store any raw image of biometric traits. for example the hybrid biometric platform from M2SYS does not store any biometric images and it is impossible to recreate the original biometric image if a hacker were to steal the biometric enrollment template. Biometric identity enrollment templates stored on a server or computers are not actually images at all. They are a mathematical representation of the data points that a biometric algorithm extracts from a scanned fingerprint, finger vein, palm vein or iris. Hope that helps to clarify.